Application Portfolios: The Silent Tax on Change - and How to Take Back Control
Application portfolios aren’t sets of projects - they’re strategic assets. Unmanaged variation creates a silent tax on change: higher costs, slower delivery, rising risk, and vendor dependency. Treating applications as a portfolio restores control and execution speed.
An application landscape is a portfolio, not a set of one-off projects. Treating it like a portfolio makes risk visible and manageable. Treating it like a series of individual solutions creates silent, compounding drag: slower delivery, higher cost, and growing operational and vendor dependency.
Unmanaged variation becomes a hidden tax on change. It rarely triggers one dramatic failure. Instead, it steadily reduces speed, control, and confidence - until business goals become difficult to execute reliably.
This is not primarily a technology problem. It is a strategy and governance problem - with business outcomes.
Executive summary
Most application portfolios are not “too complex” because they have many systems. They become costly because they accumulate unmanaged variation.
What unmanaged variation creates:
- Higher cost per change
- Longer delivery timelines
- Reduced resilience and reliability
- More security and operational risk
- Growing dependency on vendors or a few individuals
- Slower, more expensive cloud migration and modernization
The leadership answer is simple:
- Standardize foundations
- Manage applications by lifecycle intent
- Establish portfolio-level ownership and decision-making
- Require vendors to operate inside your model
1) What executives actually care about (and what they don’t)
The core issue is not “technology diversity” by itself. The issue is what diversity produces for the business:
- Delivery slows down because every application works differently
- Costs rise because each change requires more coordination and specialist work
- Risk grows because operational and security practices become inconsistent
- Dependency increases because knowledge becomes siloed and scarce
Executives rarely ask for fewer programming languages or versions. They ask why every initiative takes longer than expected - and why outcomes feel less predictable.
Portfolio complexity is often the root cause, whether it is named or not.
2) Portfolio problems are slow-moving, high-impact
Application portfolio complexity is dangerous because it is easy to ignore.
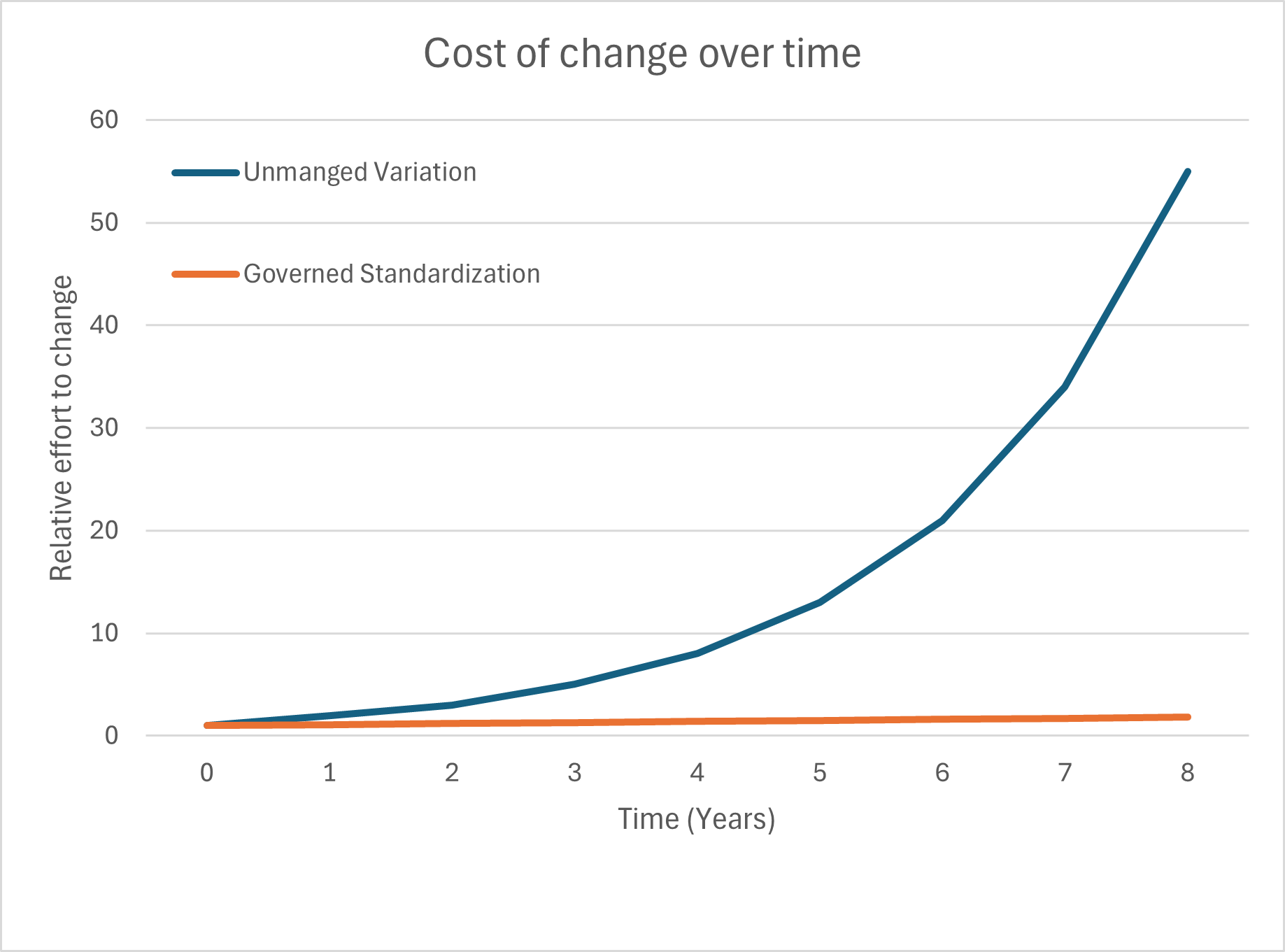
It doesn’t typically cause immediate breakdown. It creates a permanent tax on every initiative:
- Every change requires more people
- Every release needs more coordination
- Every integration takes longer
- Every migration becomes more expensive
- Every vendor adds more variation
- RFPs more complex than necessary
This is why the impact is large yet slow: the portfolio consumes time, budget, and leadership capacity until it limits what the business can achieve.
3) Define the problem in executive language: unmanaged variation
Many organizations can handle complexity when it is intentional and governed. The real problem is unmanaged variation - when every application becomes its own world:
- Differences in the common foundation
- Different architectures and design patterns
- Different operational models
- Different documentation and support expectations
- Different security assumptions
- Different deployment and release processes
At that point, your portfolio is no longer “a set of applications.”
It becomes a set of individually negotiated exceptions.
That is not scalable.
4) Standard foundations are industrialization
Most portfolios suffer because applications were built as isolated solutions rather than as part of a coherent production system.
A shared foundation - whether called a platform, standard foundation, reference architecture, or standardized building blocks - is not a technical luxury. It is an operational necessity when software becomes a core capability.
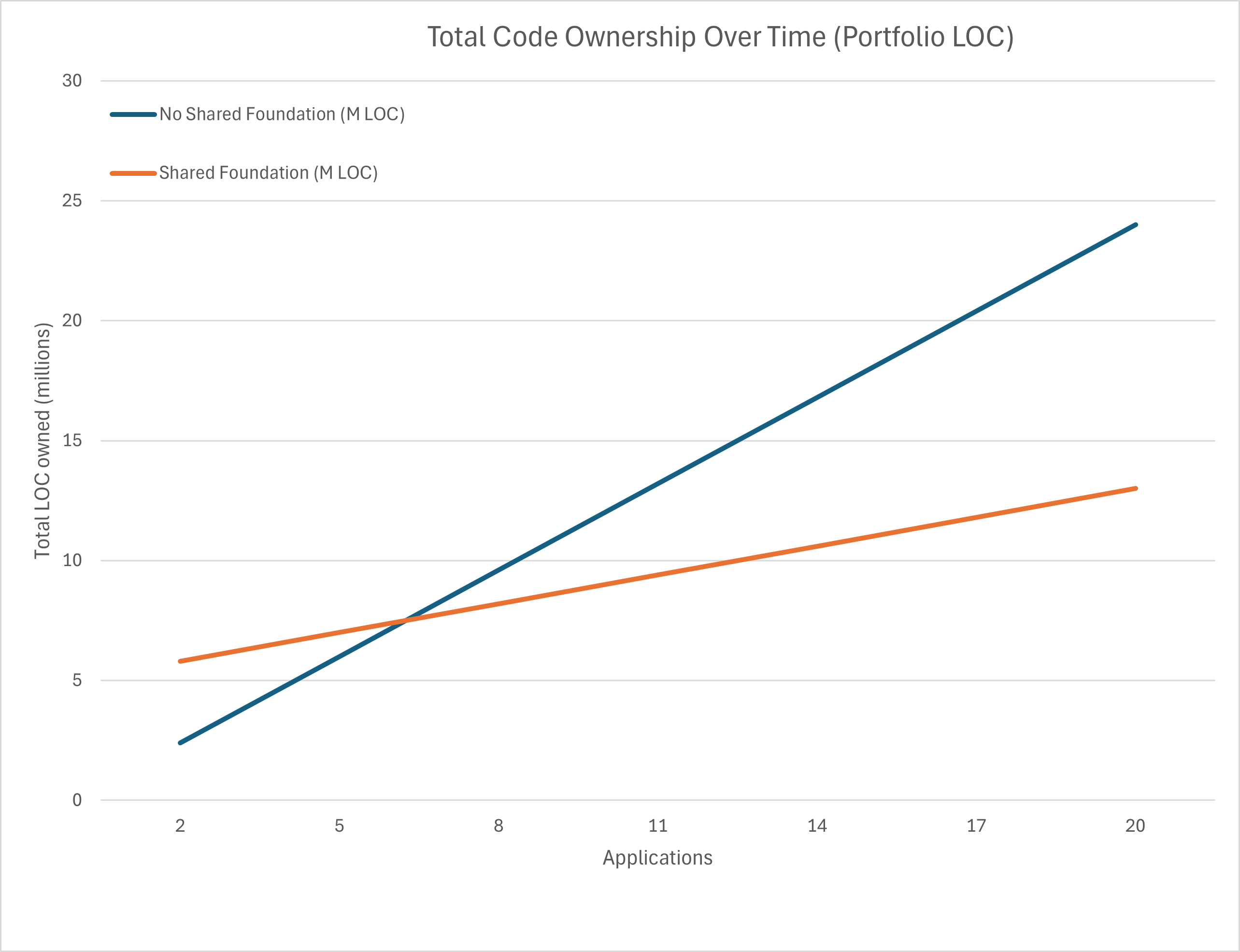
Shared foundations enable:
- Repeatability – teams deliver in proven, standardized ways
- Predictability – consistent timelines, costs, and outcomes
- Efficiency – effort focuses only on domain-specific needs per application
- Maintainability – fewer specialists required and fewer one-off fixes
- Security and compliance by design – controls applied consistently, not retrofitted
- Quality by design – quality is built in, not reinterpreted per vendor or project
- Scalable efficiency – improvements benefit many systems, not just one
This is the shift from custom craftsmanship to industrialized delivery - not because creativity is bad, but because the business needs scalable outcomes.
5) Cloud migration: complexity doesn’t disappear - it becomes visible
Cloud migration doesn’t remove portfolio complexity. It exposes it.
Applications with bespoke architectures and unique operational practices cannot be migrated efficiently. Each one requires special handling, and costs multiply.
Cloud programs slow down not because cloud is hard - but because the portfolio was never built to move as a portfolio.
Standardization is what creates migration speed.
6) The critical leadership gap: enterprise architecture vs software architecture
Many organizations have enterprise architecture (EA) practices that map:
- Business capabilities
- Applications
- Integrations
- Data flows
This visibility is valuable. But in many cases, it does not control how solutions are built and operated across the portfolio.
That missing layer is software architecture at portfolio scale, including:
- Shared foundation, components and platform services
- Delivery patterns and reference implementations
- Runtime standards and version control
- Operational practices (monitoring, logging, release)
- Lifecycle discipline and maintainability expectations
This is the gap:
- Enterprise architecture often answers “what exists and how it connects.”
- Portfolio-scale software architecture must answer “how we build and run solutions consistently.”
When this gap exists, the organization has visibility but not control.
Complexity grows even while leadership believes the portfolio is “managed.”
7) The common failure mode: optimizing projects instead of portfolio outcomes
A frequent pattern looks like this:
- A business need triggers an RFP for an application
- A vendor delivers a solution optimized for that project
- Another RFP follows for the next “unique” system
- The portfolio becomes a patchwork of incompatible approaches
- The foundation of applications are usually reimplemented
Each project can be a success in isolation.
But the organization loses long-term:
- More technologies/versions of to support
- More integration friction
- More security and compliance work
- More operational variation
- More dependency on vendors or specialist knowledge
- More and complexer maintenance - proportionate to code base
Procurement and delivery often optimize locally.
Application portfolios punish local optimization.
They require portfolio governance.
8) What leaders should measure - without getting technical
Leaders don’t need technical deep dives. They need clear indicators that show whether the portfolio is becoming an asset - or an accumulating liability.
Indicators of rising portfolio tax
- Increasing time and cost to deliver small changes
- Rising effort to maintain systems - updates, ensure systems stable and compliant
- Unproportionate effort to provide business value
- Too many “exceptions” for deployment, security, and operations
- Key systems dependent on a small number of people or one vendor
- Cloud migration timelines expanding as inventory becomes clearer
Indicators of insufficient control
- Unclear ownership for applications
- No consistent lifecycle approach (modernize / consolidate / retire)
- No enforced standards or shared foundation
- Technology versions and patterns drifting across the estate
The key leadership question is simple:
“Can we change our systems at the speed the business needs - reliably and repeatedly?”
9) The strategic choices leaders should make
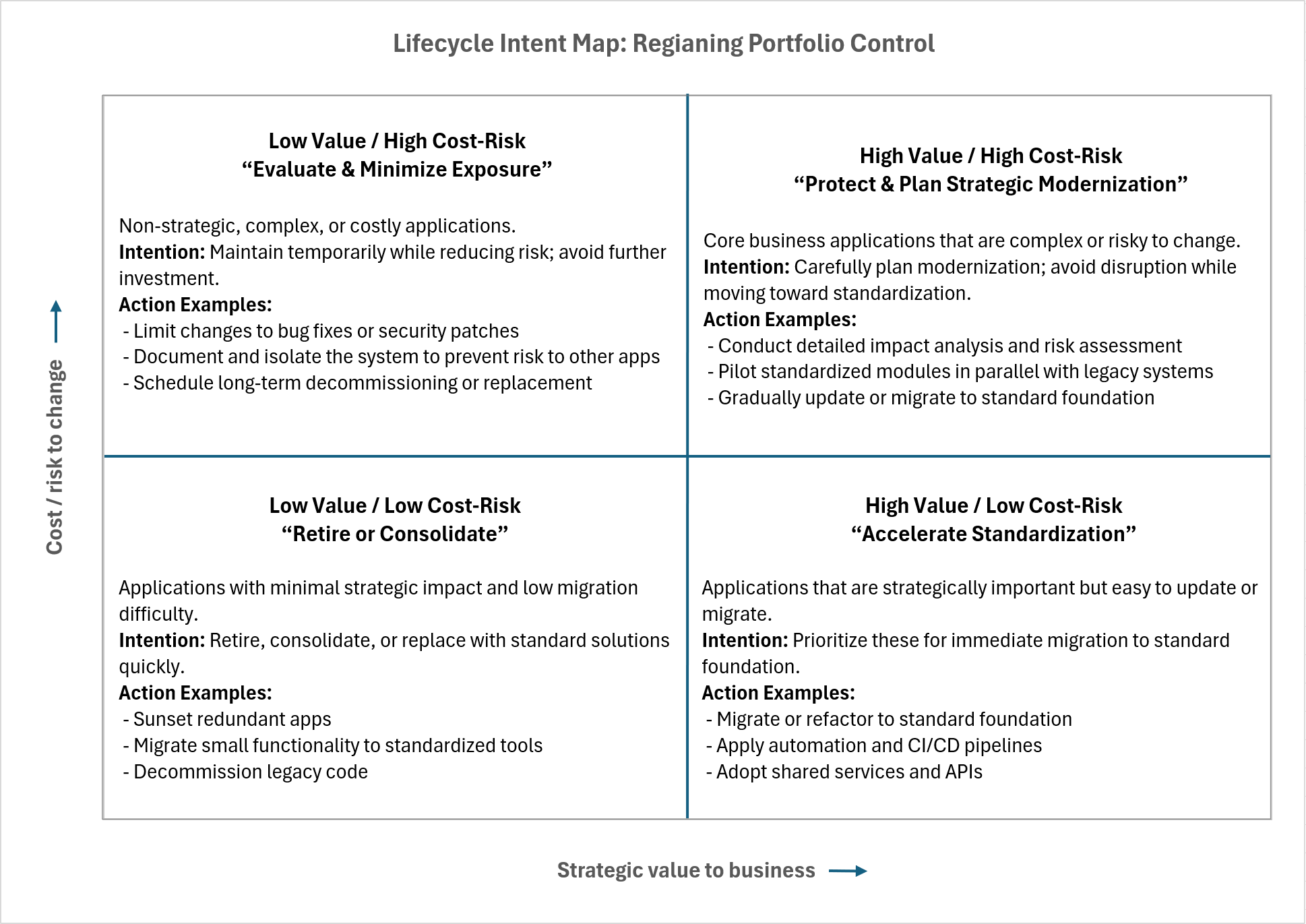
The objective is not to rebuild everything. The objective is to reduce unmanaged variation and manage the application portfolio as a deliberate investment, not an accident of history.
A practical portfolio strategy typically includes the following elements.
9.1) Standardize the foundations
Define a small, explicit set of approved building blocks and operational standards, including:
- Standard reference architectures
- Identity and access management models
- Logging, monitoring, and observability expectations
- Deployment and release patterns
- Documentation and support requirements
- Reusable components where standardization creates real leverage
For larger portfolios, this often means establishing a reusable base framework that applications build upon rather than reinvent.
The strategy should intentionally grow and evolve the standard foundation over time, enabling teams to focus on domain-specific differentiation while relying on shared, proven capabilities for everything else.
This organization took years to reach its current state. Implementing a disciplined portfolio strategy will also take time. Progress comes from consistent enforcement, incremental adoption, and clear leadership commitment - not from a single transformation effort.
9.2) Manage applications by lifecycle intent
For each application, based on business value and cost to change, position intent.
9.3) Define ownership that persists beyond projects
Portfolio-level ownership prevents long-term drift:
- Who owns the shared foundation
- Who defines standards and enforces compliance
- Who owns lifecycle decisions
- Who approves new additions to the portfolio
9.4) Ensure vendors operate inside your model
Vendors are not the problem.* Weak governance is.
*A structural conflict of interest exists when vendors are paid by the hour for implementation and ongoing maintenance. This model rewards complexity over sustainability. In addition, your vendors must operate at a higher skill level: you are not building a one-off “vehicle,” but a platform - much like in the automotive industry - where multiple models are produced from shared components, diverging only where it truly matters.
Effective outsourcing therefore requires:
- Use of standardized foundations as the default, not the exception
- Clear adoption and compliance rules for shared foundations
- Reference architectures, implementations, and mandatory patterns to guide delivery
- Measurable quality and maintainability targets, not subjective assessments
- Operational accountability, with ownership extending beyond delivery
Vendors must adapt to your platform model - not redefine it.
10) A structure leadership can act on
A strong response is not “launch a huge program.” It is a staged approach that restores control early.
First 30–60 days: establish visibility and control
- Inventory applications and owners
- Identify the most expensive points of change
- Define baseline standards (“minimum industrialization”)
- Stop adding new unmanaged variation
Next 3–6 months: build foundations and governance
- Build or adopt shared foundations as a product
- Establish portfolio decision-making (not project-by-project)
- Redesign RFPs to require alignment with portfolio standards
- Consolidate obvious duplicates and high-cost exceptions
Next 6–18 months: modernize with portfolio intent
- Reduce the number of unique ways systems are built and run
- Accelerate cloud migration through standardization
- Improve reliability and delivery speed through reuse
- Create predictable delivery capacity across teams and vendors
Closing: portfolio strategy is business strategy
Application portfolios are no longer “IT inventory”. They are the machinery through which modern businesses execute change.
When portfolios grow without shared foundations and portfolio-level ownership, the organization pays a rising, silent tax: slower delivery, higher cost, more dependency, and less control.
Managed strategically, the portfolio becomes the opposite: a scalable capability that enables the business to move faster - with confidence.
That is the real goal:
Reliable change at the speed of business.
